AWS Transit Gateway is one of the most important services to understand if you want to build scalable AWS networking without turning your cloud architecture into a maze of manual connections. Many AWS environments start simple, with one or two VPCs and maybe a VPN back to on-premises infrastructure. But the moment your organization grows, launches multiple environments, or separates workloads across accounts, networking complexity can explode.
That is exactly where AWS Transit Gateway becomes valuable. Instead of connecting everything to everything else individually, it gives you a centralized networking hub that simplifies connectivity across Amazon VPCs, site-to-site VPNs, Direct Connect, and even multiple AWS accounts. If you are preparing for AWS certification, designing enterprise cloud architecture, or simply trying to clean up an overly complicated network, understanding AWS Transit Gateway can save you from expensive mistakes later.
This article transforms the core ideas from the original guide into a deeper, more practical resource with an architecture-first perspective. Rather than just explaining what the service does, we will look at why it matters, where it fits, when it is the right tool, and how to avoid common design pitfalls. The source transcript focuses on AWS Transit Gateway as a solution for complex network topologies and hybrid connectivity, including route control, VPN scaling with ECMP, and cross-account networking.
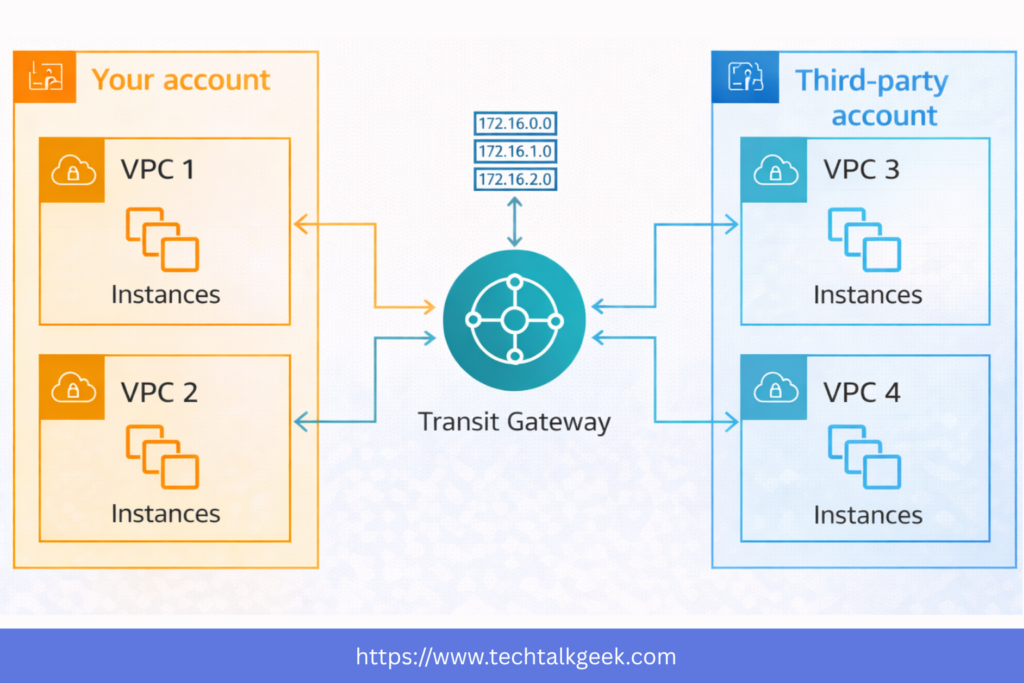
Table of Contents
What Is AWS Transit Gateway?
AWS Transit Gateway is a regional network transit hub that allows you to connect multiple VPCs and on-premises networks through a single central gateway. Think of it as a cloud router designed for scale. Instead of building dozens of one-to-one connections between VPCs or manually managing overlapping network relationships, you connect each network attachment to the transit gateway and manage traffic centrally.
At a high level, this changes your architecture from a web of point-to-point connections into a hub-and-spoke model. That shift may sound small, but operationally it changes everything. Network management becomes cleaner, routing becomes more consistent, and scaling your AWS environment becomes much easier.
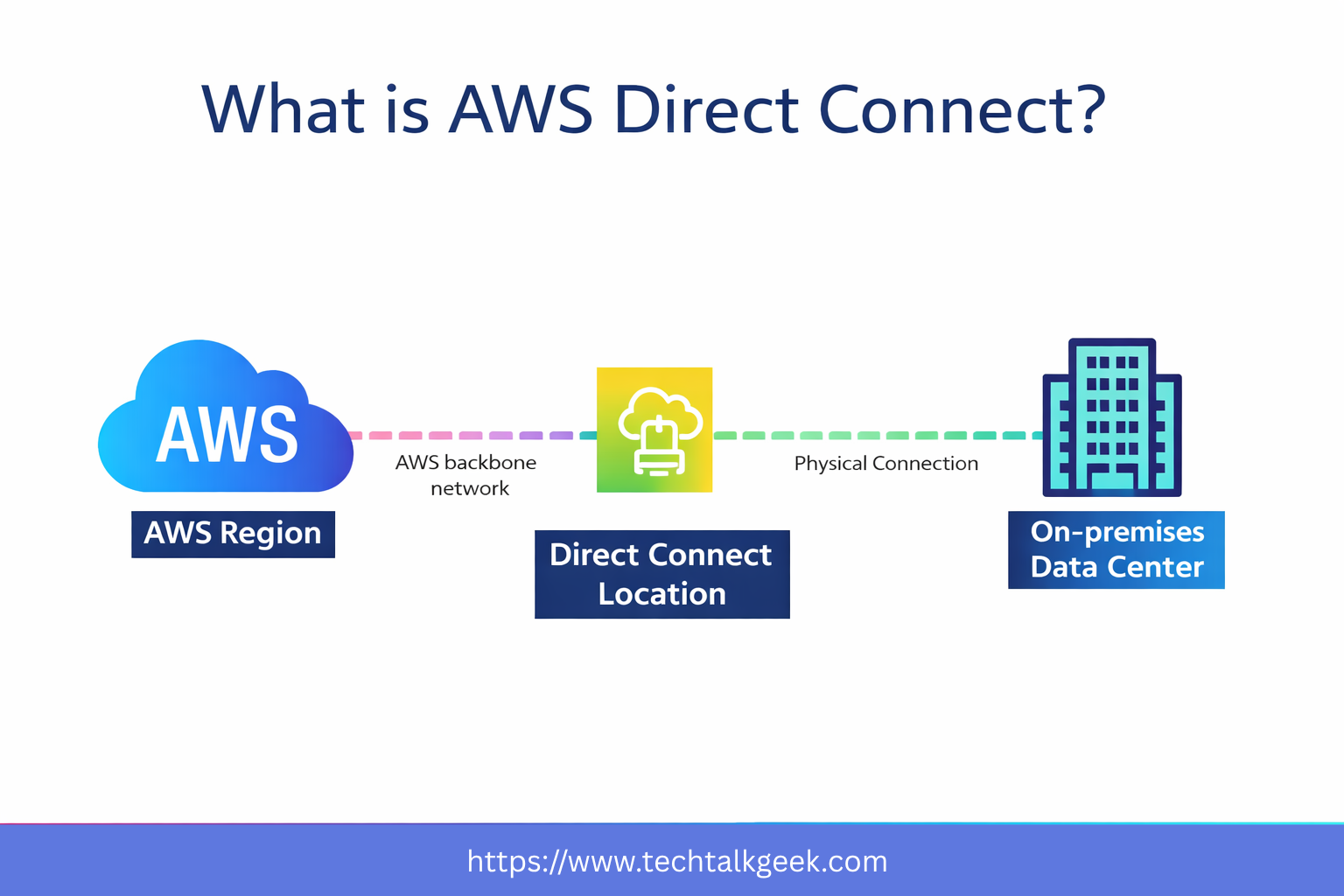
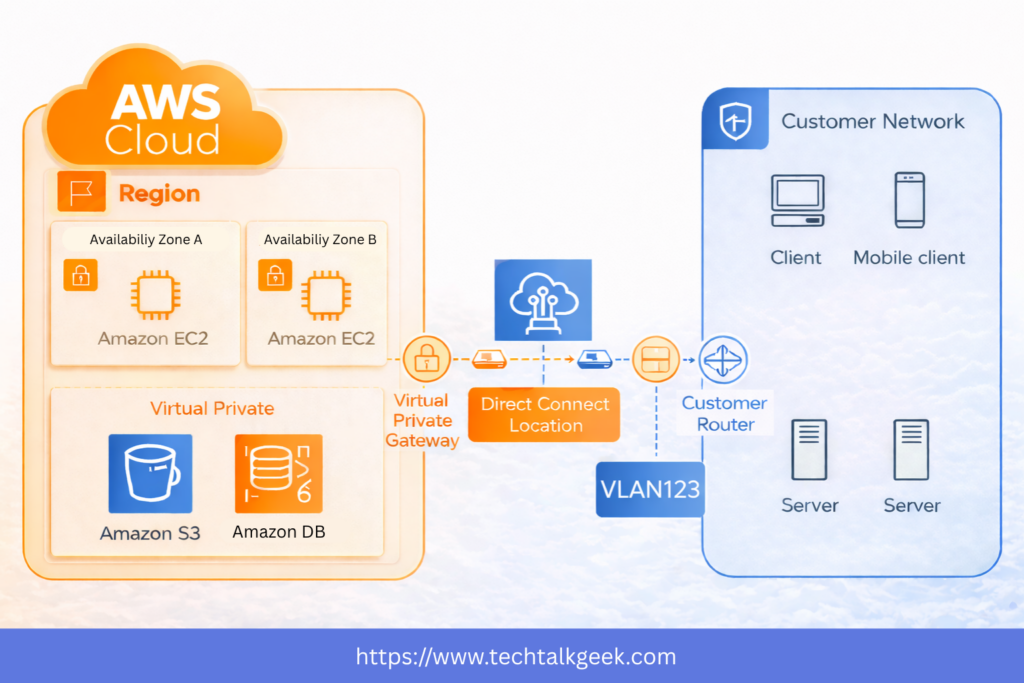
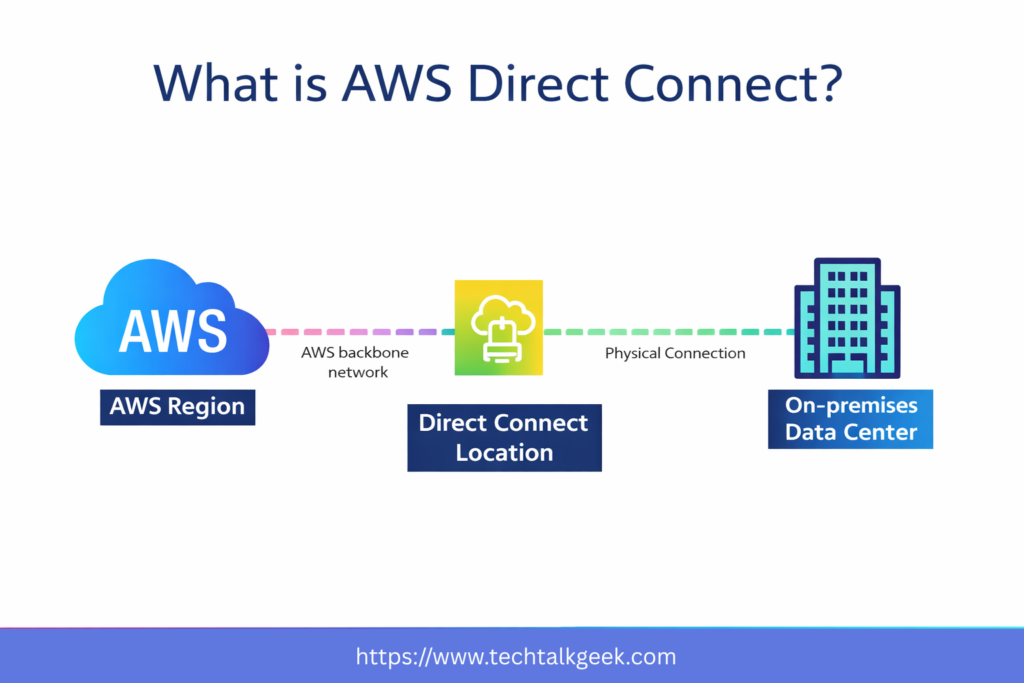
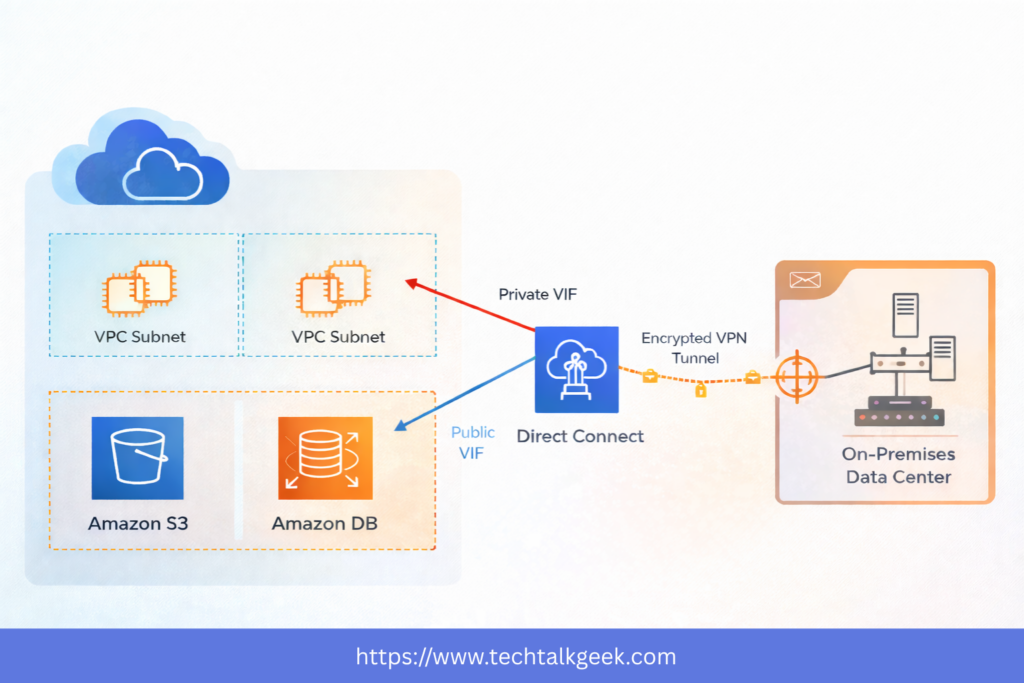
This is especially useful in organizations that run multiple VPCs for development, production, testing, shared services, logging, or security segmentation. It is also highly relevant in hybrid cloud environments where AWS must communicate with a corporate data center using VPN or Direct Connect. The original transcript emphasizes that AWS created Transit Gateway specifically to solve this growing topology problem when organizations start connecting many VPCs, VPNs, and Direct Connect resources together.
Why Traditional AWS Networking Becomes a Problem
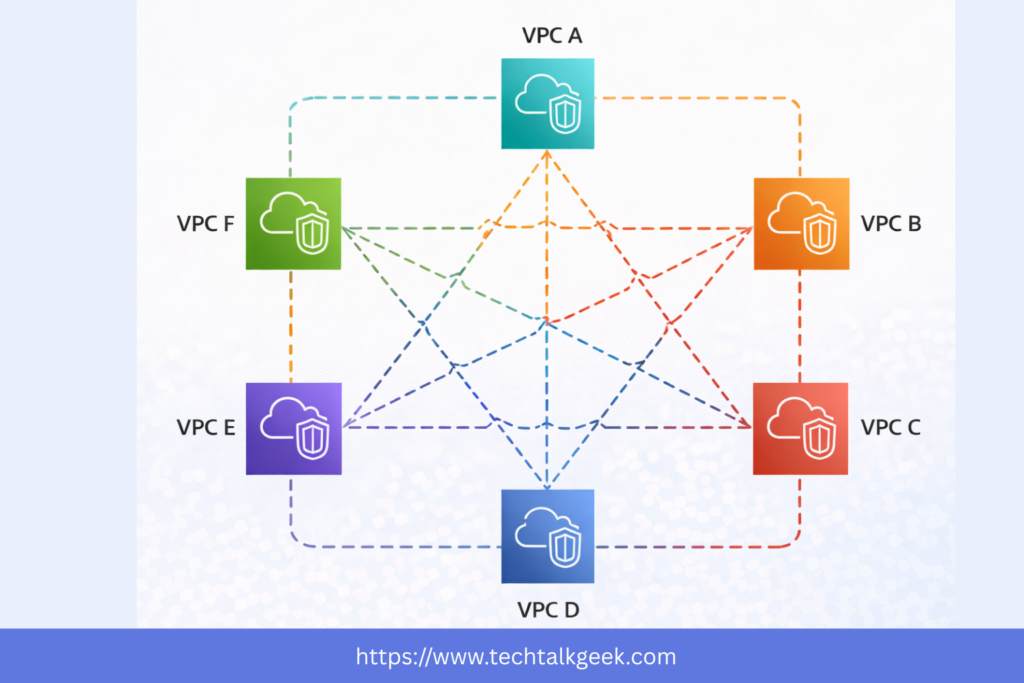
A lot of AWS networking pain starts with a design that seemed reasonable at first. You launch one VPC for your application, another for staging, and maybe a third for analytics. Then you need them to talk to each other. So you add VPC peering. Later, your company adds a second AWS account, and then an on-premises office wants access too. Soon, you are juggling peering relationships, route tables, VPN attachments, and access rules scattered across multiple environments.
This becomes hard to manage for three reasons. First, point-to-point connectivity does not scale cleanly. Every new network can create several new relationships. Second, routing logic becomes fragmented across multiple places. Third, visibility suffers. It becomes difficult to answer simple but critical questions, such as which network can reach production databases, which account has on-prem access, or whether staging accidentally has broader connectivity than intended.
AWS Transit Gateway addresses this by centralizing the network core. Instead of thinking in terms of one-off links, you think in terms of attachments and controlled routing domains. That makes your architecture more intentional and much easier to grow.
This is where many teams realize that AWS Transit Gateway is not just a connectivity tool. It is a governance tool. It gives you a cleaner way to structure network access as your environment evolves.
How AWS Transit Gateway Actually Works
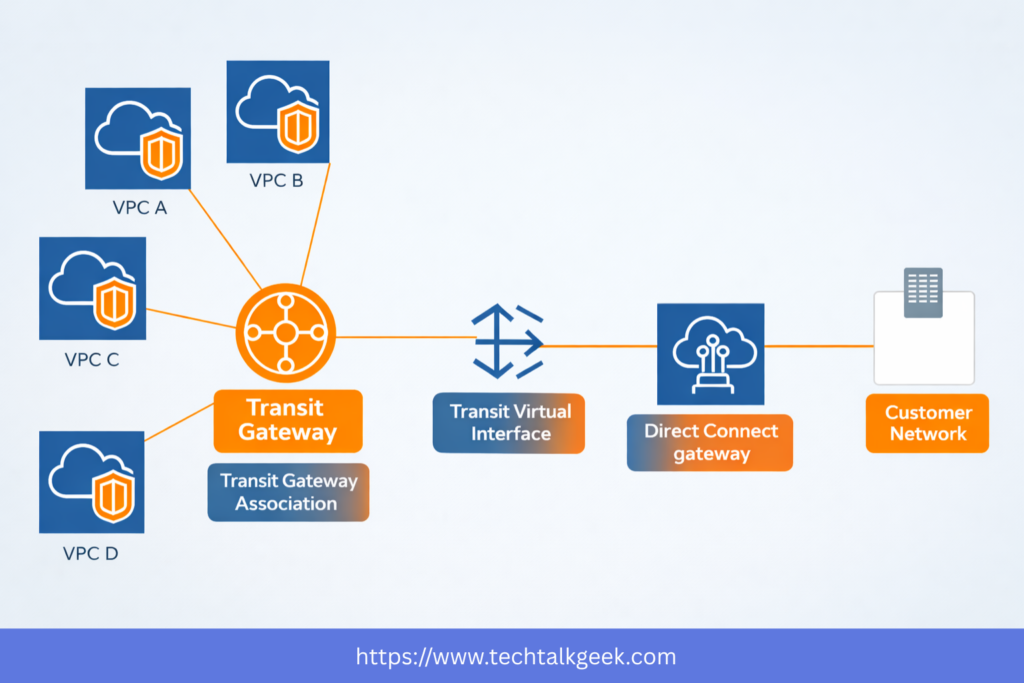
At the center of the design is the transit gateway itself. You attach VPCs to it, and those VPCs can then communicate with other attached networks depending on how your routing is configured. You can also attach site-to-site VPN connections, Direct Connect gateways, and even peer transit gateways across regions.
That means a single AWS Transit Gateway can become the networking core for a wide range of cloud and hybrid traffic patterns. For example, a production VPC, shared services VPC, security inspection VPC, and logging VPC can all be attached to the same central hub. If you also need your on-premises data center to reach those environments, you can connect it through VPN or Direct Connect without building separate connectivity for every VPC.
One of the most important conceptual shifts here is that connectivity is not automatically equal to unrestricted access. Just because networks are attached to the same AWS Transit Gateway does not mean they should all communicate freely. The real power of the service comes from how you manage traffic between those attachments.
That distinction matters a lot in real-world architecture. Good cloud networking is not just about making things reachable. It is about making the right things reachable and nothing more.
AWS Transit Gateway for Hybrid Cloud and Multi-Account Architectures
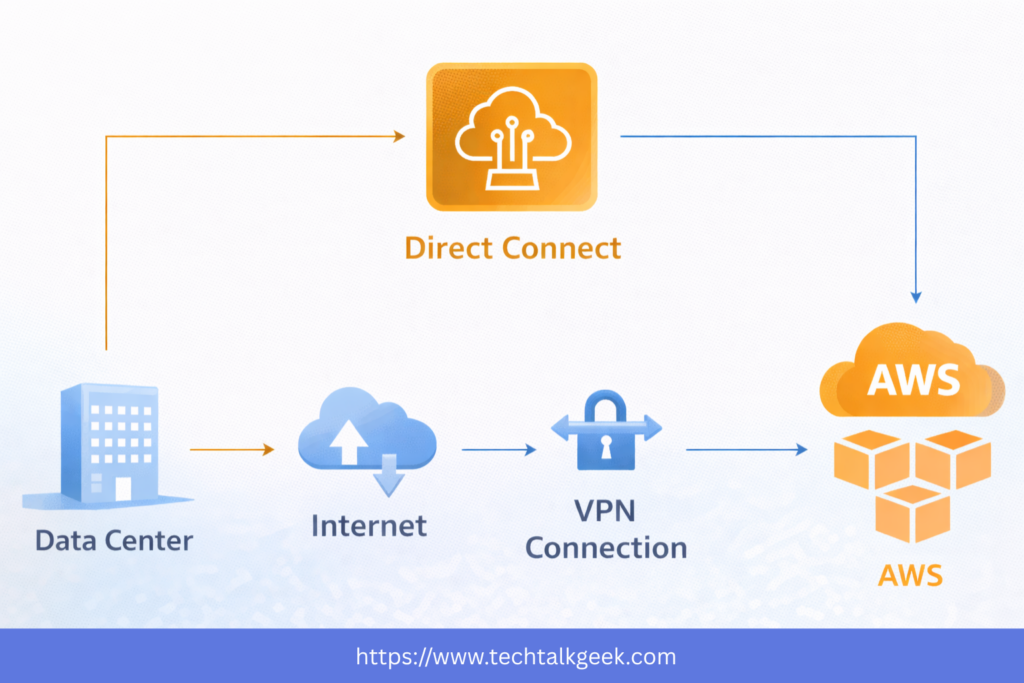
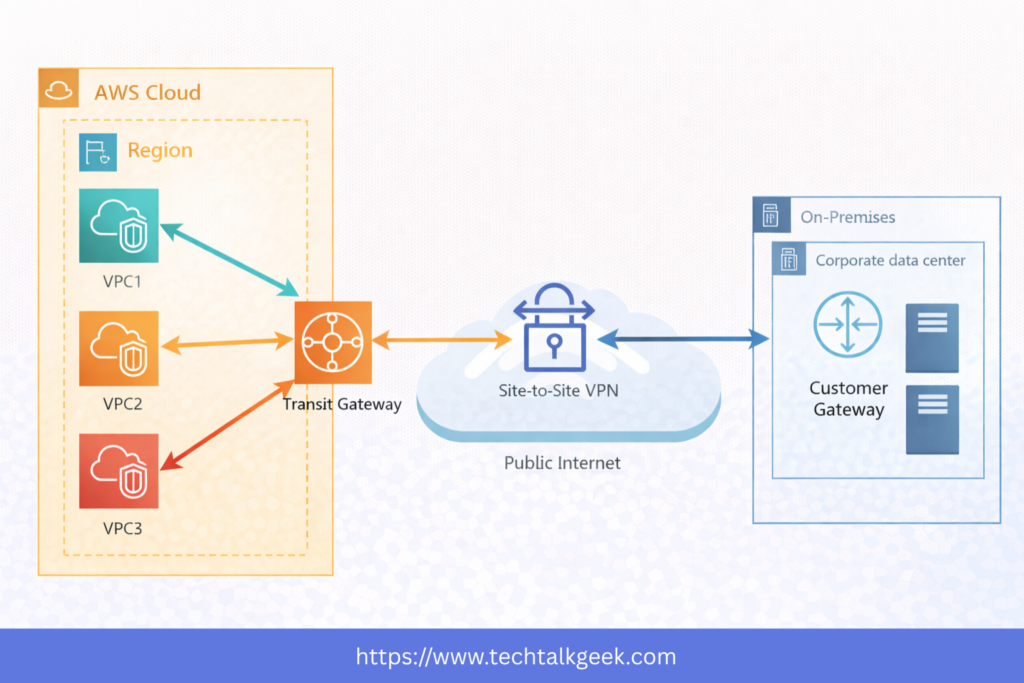
One of the strongest use cases for AWS Transit Gateway is hybrid cloud. Many businesses are not fully cloud-native. They still run legacy systems, internal tools, or compliance-sensitive workloads in a corporate data center. In those cases, AWS is not replacing the data center overnight. It is extending it.
This is where Transit Gateway becomes strategically useful. Instead of building separate VPNs or separate private connectivity into each VPC, you can connect your on-premises environment to AWS Transit Gateway and allow controlled access to multiple VPCs from one central point. That simplifies operations and reduces the number of moving parts in your network design.
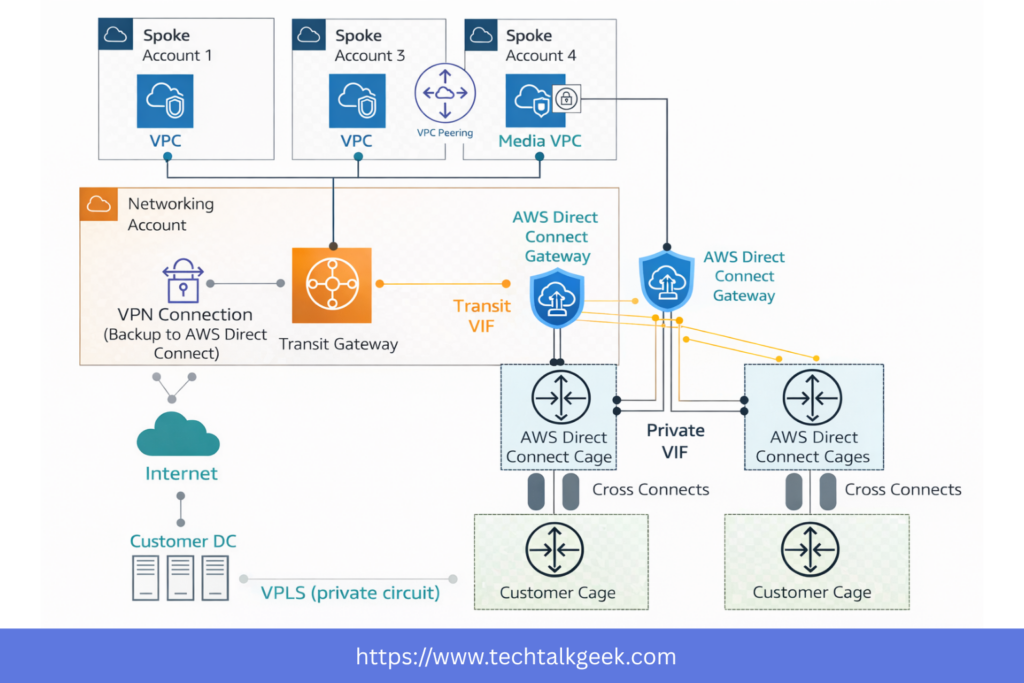
It also becomes highly valuable in multi-account AWS environments. Modern AWS best practices often recommend separating workloads into different accounts for billing, security, and operational isolation. But once you do that, you still need secure communication between some of those environments. AWS Transit Gateway gives you a practical way to share connectivity across accounts without building a tangled web of custom interconnections.
You can share a transit gateway across accounts using AWS Resource Access Manager, and that you can also connect a Direct Connect Gateway into Transit Gateway to make private connectivity available across multiple VPCs and accounts.
For official AWS documentation on this architecture, you can reference the AWS Transit Gateway documentation here: AWS Transit Gateway Documentation.
You can also review AWS Resource Access Manager here: AWS RAM Overview.
If you want AWS Direct Connect: AWS Direct Connect
Routing, Security, and Traffic Control in AWS Transit Gateway
This is the part many beginners underestimate. AWS Transit Gateway is not just about plugging networks together. It is about controlling how traffic flows between them.
The core mechanism for that control is the transit gateway route table. These route tables determine which attachments can send traffic to which destinations. This allows you to create segmentation policies inside your AWS network backbone.
For example, you may want your shared services VPC to be reachable by both development and production. Still, you do not want development and production to communicate directly with each other. With AWS Transit Gateway route tables, that becomes possible without building awkward workarounds.
This also makes AWS Transit Gateway useful from a security architecture perspective. You can isolate environments, control east-west traffic, and build centralized inspection or egress patterns. In mature cloud environments, networking and security design increasingly overlap, and Transit Gateway often sits right in the middle of that intersection.
The original guide points out that route tables inside Transit Gateway are what allow you to define who can talk to what and to maintain control over traffic paths across connected environments.
A common mistake is assuming Transit Gateway is a plug-and-play “connect everything” service. In reality, the best designs are intentional. Your routing should reflect your application boundaries, trust zones, and operational responsibilities.
AWS Transit Gateway and VPN Performance with ECMP
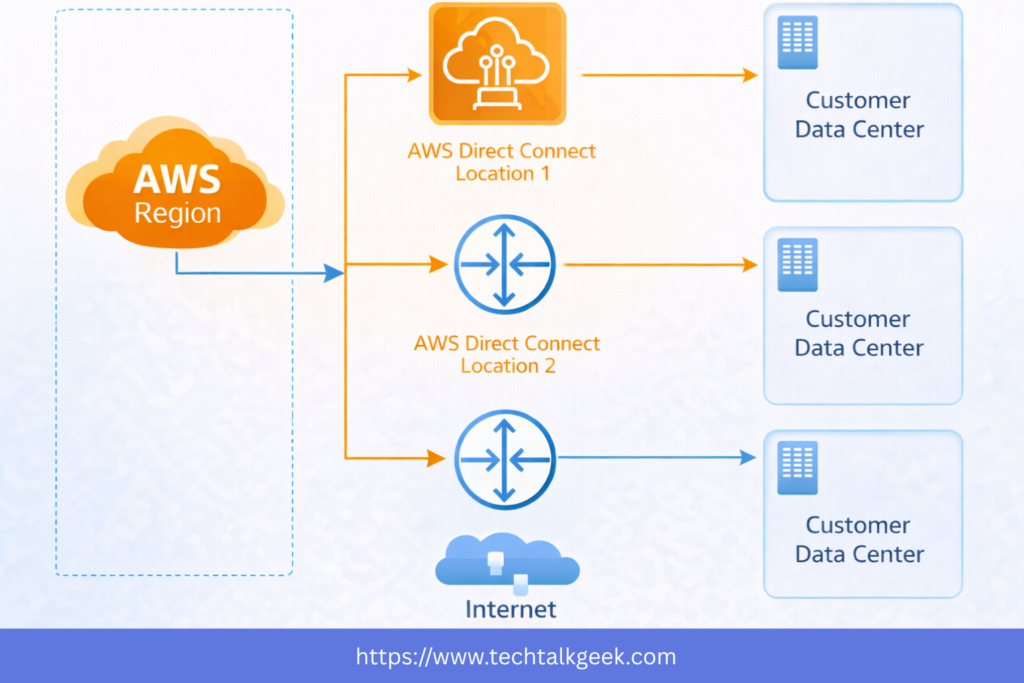
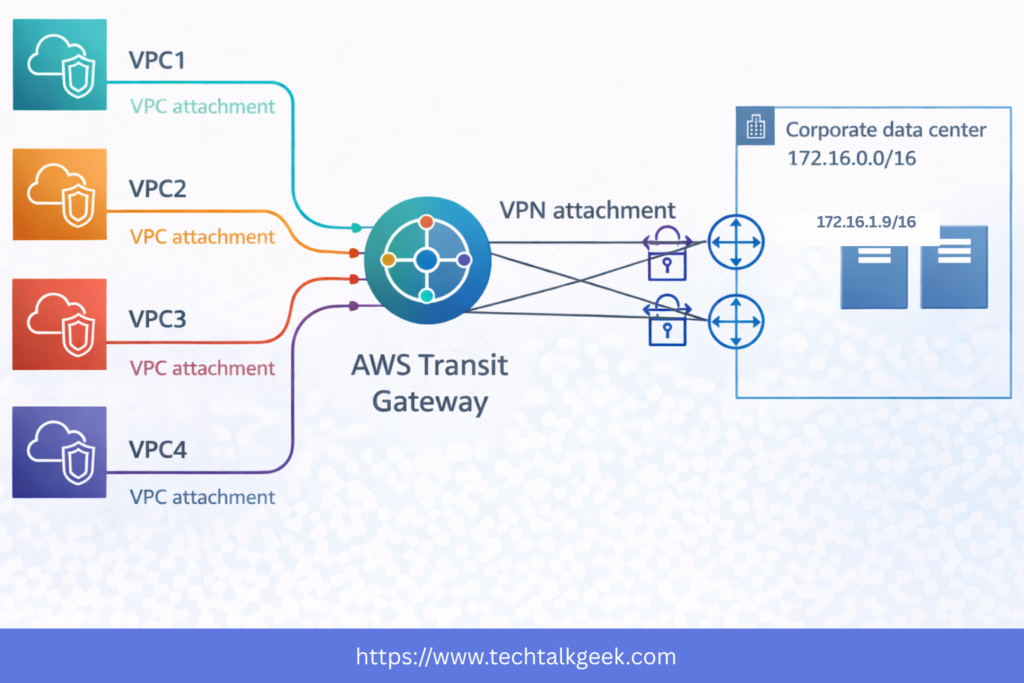
One of the more advanced and valuable AWS Transit Gateway use cases involves improving VPN throughput using Equal-Cost Multi-Path routing, commonly known as ECMP.
This is where AWS Transit Gateway becomes more than just a convenience. It can also become a performance enabler.
In a standard AWS site-to-site VPN setup connected directly to a Virtual Private Gateway, your VPN connection includes two tunnels. Still, the design is limited in how traffic uses them. With AWS Transit Gateway, ECMP allows traffic to be distributed across multiple equal-cost paths, which can improve throughput and resilience when configured properly.
This matters for organizations that rely on VPN as a practical alternative to Direct Connect, especially during migration phases or in environments where private connectivity is not yet available. Instead of being restricted to a single narrow path into one VPC, you can terminate VPN into AWS Transit Gateway and extend controlled access across multiple attached VPCs.
VPN connecting to the Transit Gateway can leverage ECMP, and multiple VPN attachments can be used to increase throughput to AWS, which is something not achieved the same way when connecting directly into a single VPC through a Virtual Private Gateway
That said, there is an important practical note here: more throughput often means more cost. AWS Transit Gateway charges for both attachments and data processing, so architectural simplicity and bandwidth gains should always be weighed against your traffic profile.
For deeper technical reference, AWS provides official guidance on ECMP and VPN design here: AWS Site-to-Site VPN Tunnels.
When to Use AWS Transit Gateway vs VPC Peering
This is one of the most useful design questions you can answer early.
If you only have two or three VPCs and their connectivity requirements are simple, VPC peering may be enough. It is straightforward, low-friction, and often sufficient for small architectures. But the moment your network begins to grow, AWS Transit Gateway starts becoming the cleaner long-term option.
The tipping point usually appears when one or more of the following become true: you need centralized routing, you have hybrid connectivity, you want multi-account networking, or you need structured segmentation between environments. Those are all signs that you are no longer dealing with a “small network” problem.
In practice, VPC peering is often tactical. AWS Transit Gateway is strategic.
That distinction can save teams from painful re-architecture later. Many environments start with peering because it feels simpler, but then outgrow it quickly. If you already know your AWS footprint will expand, adopting AWS Transit Gateway earlier can reduce future migration complexity.
Common Mistakes to Avoid
One of the biggest mistakes teams make with AWS Transit Gateway is deploying it without a routing strategy. The service itself is not difficult to create, but a poorly planned route table design can quietly introduce over-permissive access, asymmetric traffic paths, or operational confusion later.
Another common issue is treating all VPCs as equal peers. In reality, not every environment should have the same network trust level. Production, development, security tooling, shared services, and logging often need different communication patterns. If you ignore that and connect everything with broad access, you lose one of the biggest advantages of AWS Transit Gateway.
A third mistake is overlooking cost. AWS Transit Gateway is powerful, but it is not a free architecture. You pay for attachments and data processing, which means heavy east-west traffic or centralized traffic inspection patterns can become expensive if not planned carefully.
Finally, some teams misunderstand its regional nature. AWS Transit Gateway is a regional service, which means cross-region design requires additional planning, such as inter-region transit gateway peering. The transcript mentions that Transit Gateway is regional but can work across regions through peering, which is an important detail for global architectures.
Good design with AWS Transit Gateway is not about using every feature. It is about using the right subset of features to match your operational reality.
Final Thoughts
AWS Transit Gateway is one of those services that looks simple on the surface but becomes incredibly valuable as your architecture grows. At first glance, it is just a central networking hub. But in real environments, it becomes the foundation for scalable cloud networking, hybrid connectivity, multi-account communication, and security-aware traffic control.
If you are building beyond a basic AWS setup, learning AWS Transit Gateway early will pay off. It helps you move away from fragile one-off connections and toward a cleaner, more intentional network architecture. And if you are preparing for AWS certification, it is also one of those services that shows up in scenario-based questions because it solves a very real architectural problem.
The original transcript gives the core exam-focused explanation: AWS Transit Gateway simplifies complex AWS networking, supports transitive connectivity between VPCs and hybrid resources, enables route-based control, works with Direct Connect and VPN, supports IP multicast, and can improve VPN throughput using ECMP.
In practice, though, its real value is even bigger than the exam. It gives you a way to scale your AWS network without scaling your complexity at the same time.